Scam Teardown Five patterns. Real evidence. All caught.
Found these on TikTok, Facebook, Email — and Meta's own AI platform. 7 fraudulent loan accounts. Pig butchering traps. A recovery scam re-victimising prior victims. And 98 sessions where Meta AI became Exhibit A. FraudShield-AIT™ catches every one. How many people lost money before anyone flagged them?
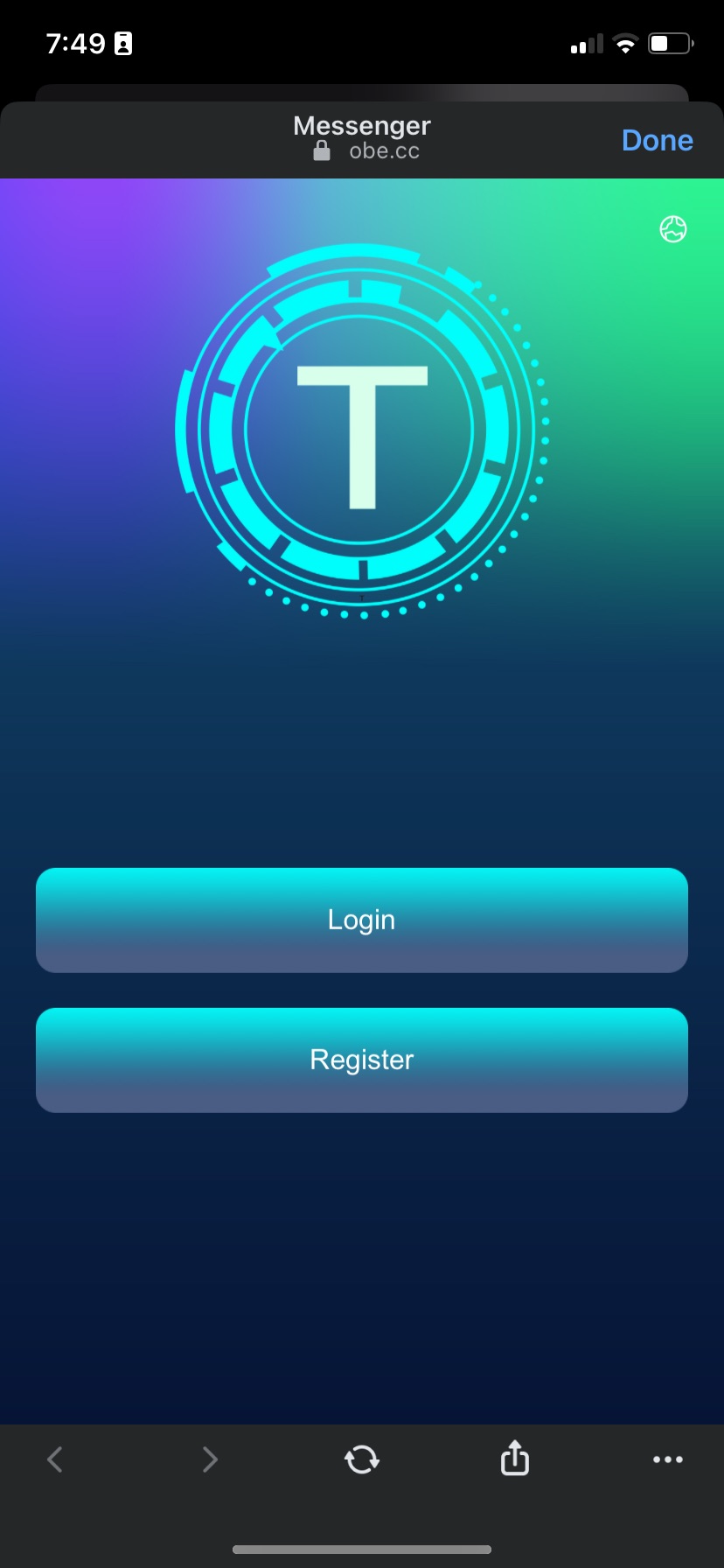
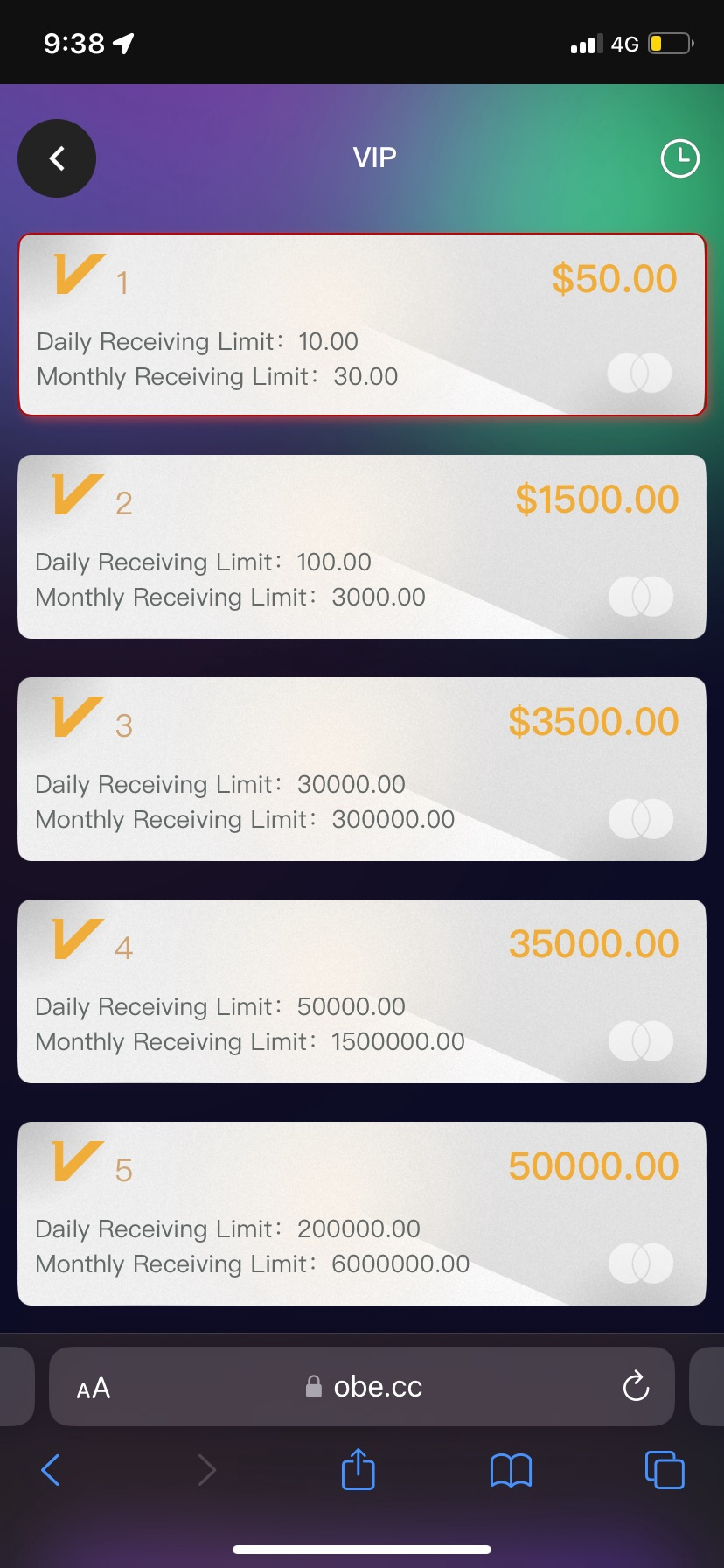
Platform: obe.cc
Three Accounts. Zero Withdrawals.
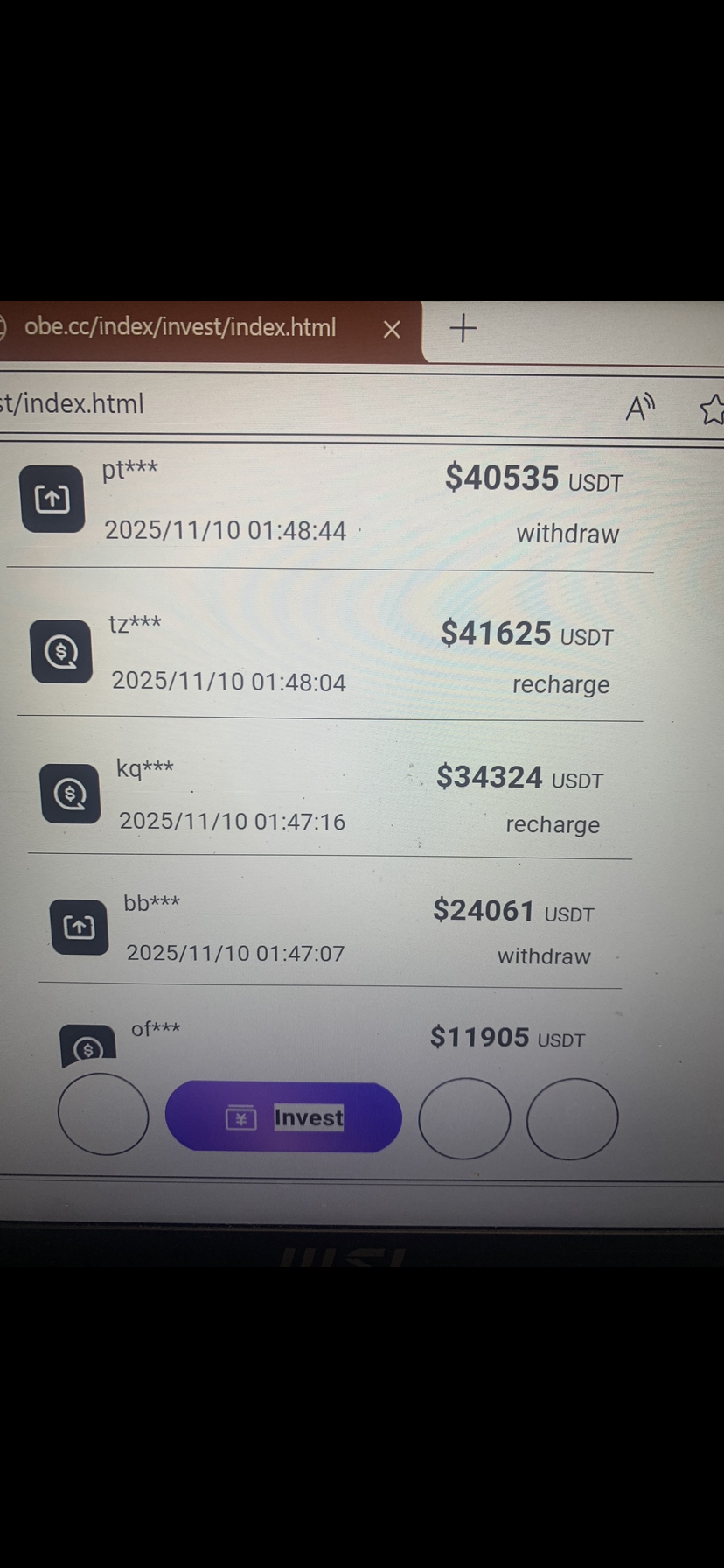
Fake crypto investment platform sourced from TikTok. Accepts deposits across three accounts, never allows a single withdrawal. Classic one-way valve.
- Disposable domain: obe.cc — no corporate registration, untraceable TLD
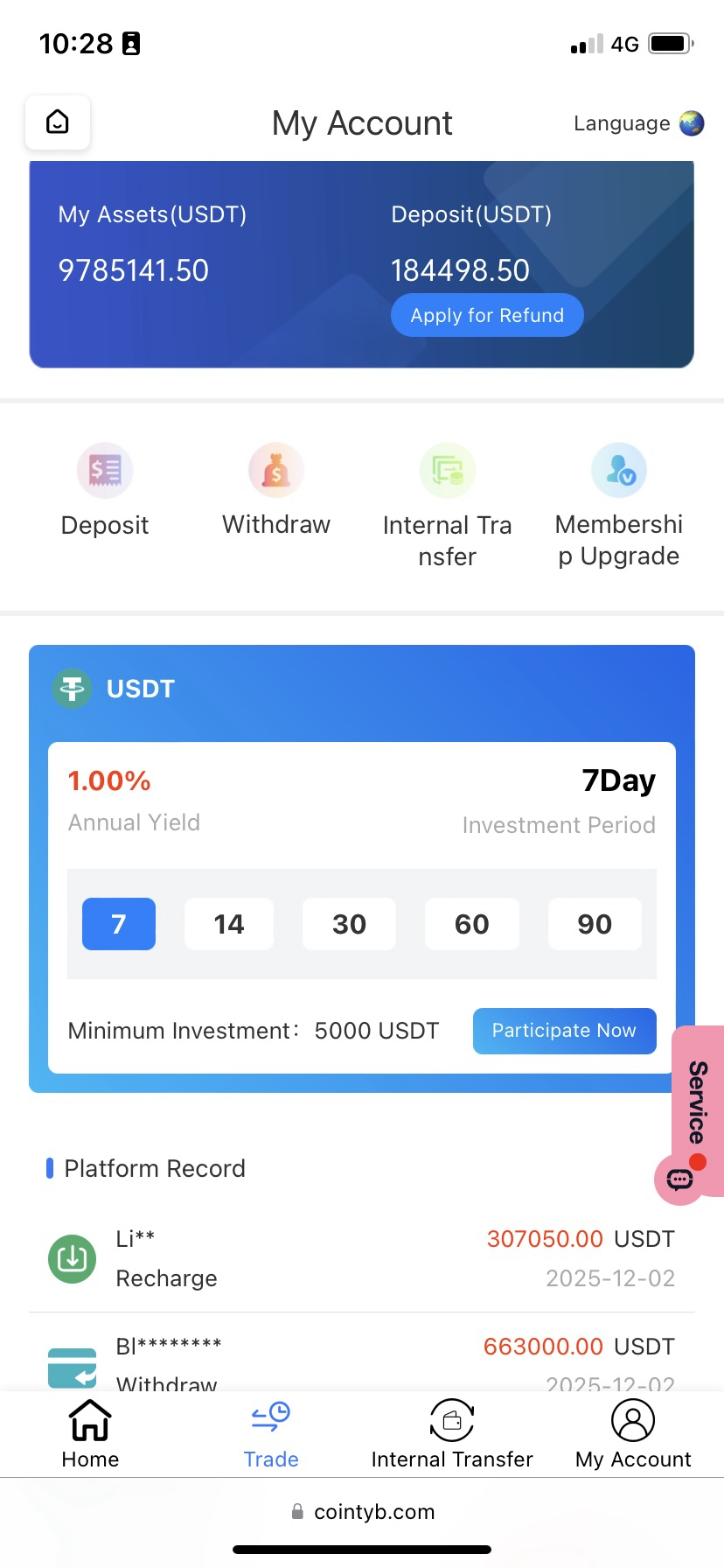
- Phantom balances: 2.8M / 9.7M USDT shown with no blockchain verification
- Fake transaction feed: Fabricated "platform records" showing constant withdrawals to build false trust
- VIP tier escalation: Deposit ladder $50 → $1,500 → $3,500 → $35K → $50K designed to extract more
- TRC20-only withdrawals: Crypto-only = untraceable = no chargebacks
- Handling fee trap: 1.5 USDT fee makes withdrawals seem possible. They're not.
- Investment lock-in: 7–90 day lock periods — stall tactics while extracting more deposits
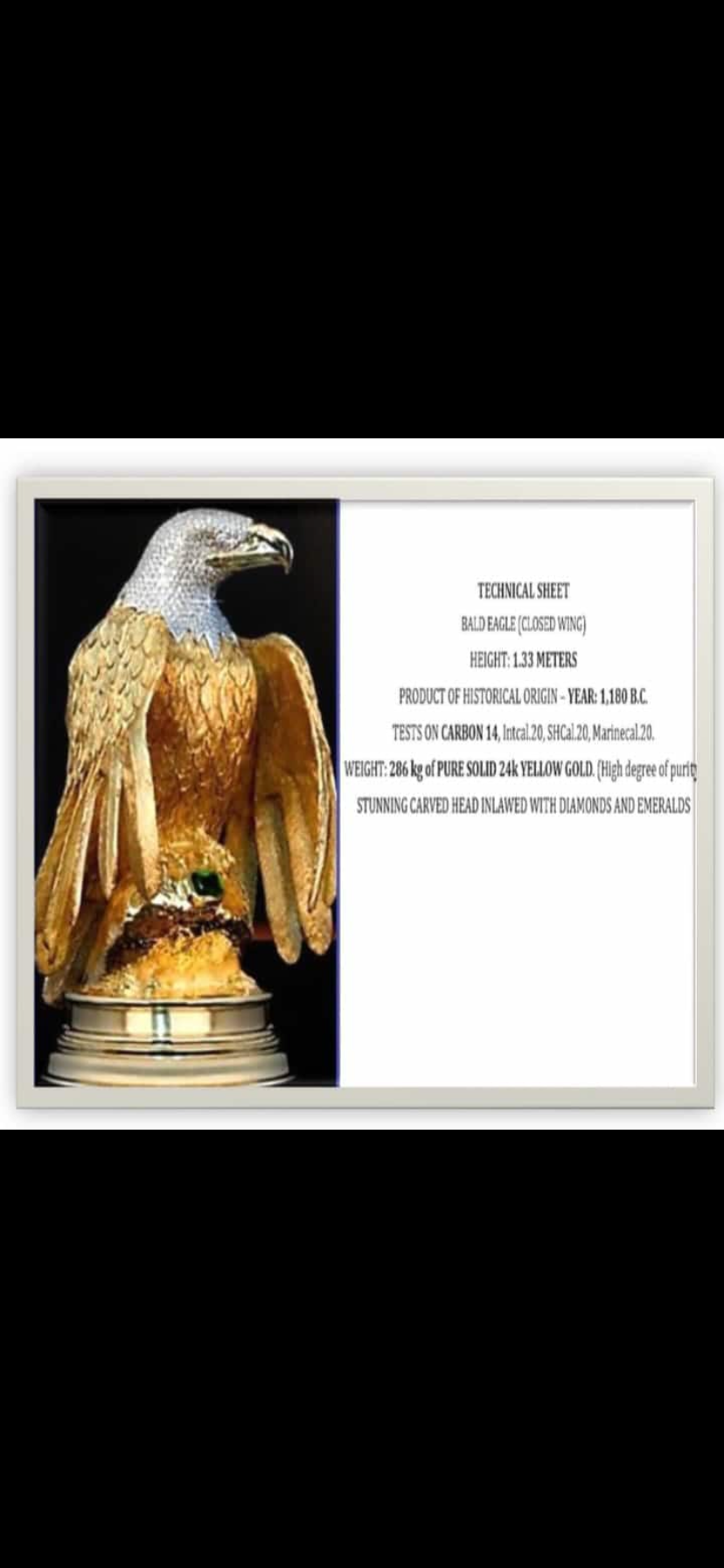
- Gold eagle artifact: "Bald Eagle, 286kg pure 24K gold, 1180 BC" — advance-fee scam object, no provenance
- Credential harvesting: Email, password, +61 phone, wallet address — forwarded to scammer inboxes
- Usernamedud988
- Emailsaquino1577@gmail.com
- Phone+61 (Australian number)
- Target regionAustralia-specific targeting
- Wallet capturedYes — TRC20 address
- Credential useStuffed across Gmail, banking, social
The "Dying Stranger"
Classic inheritance trap
Dying person needs you to claim their estate. Just pay one fee to unlock millions. That fee leads to another fee. The money never arrives.
- Urgency + secrecy: "Dying" framing creates false urgency. Secrecy isolates victim from anyone who'd flag the scam
- Unsolicited wealth: No legitimate estate transfer starts with a cold message to a stranger
- Advance fee requests: Real estate executors never ask for fees upfront — fees come out of the estate
- Escalating demands: The pattern always spawns another "final" fee. There is no final fee.
- No provenance: Sender has no verifiable identity, no legal standing, no institutional backing
- Isolation tactics: "Don't tell anyone" = preventing the victim from hearing "this is a scam"
- Greed Millions for a small upfront fee seems rational math to a victim under pressure
- Sunk cost Each fee makes quitting feel like "losing" money already spent
- Sympathy Dying-stranger narrative triggers genuine empathy, lowering critical thinking
- Isolation No external check means no one says "this is obviously a scam"
- Avg loss (AU) $12,400 per victim — ACCC 2024
7 Fraudulent Accounts
Easy approval. No loan. Ever.
Sherwin infiltrated 7 fraudulent loan operations on TikTok and social media by playing the victim. Every account approved his application instantly. Not one loan arrived.
- Upfront fees: Legitimate AFSL/ACL lenders are prohibited from charging fees before loan disbursement
- Universal approval: "Easy approval for everyone" — no real underwriting = no real loan
- OTP as withdrawal gate: Fake security theater designed to simulate a real banking system
- Social media sourcing: No regulated Australian financial institution advertises loans via TikTok/Facebook ads
- No AFSL/ACL: Cannot offer consumer credit in Australia without Australian Credit Licence — ASIC registry returns zero matches
- Urgency pressure: "Limited time / act now" — manufactured scarcity to prevent rational deliberation
- Full identity capture: Application collects name, DOB, address, bank details, employer — used for identity theft
- Accounts confirmed7 fraudulent operators
- Platforms activeTikTok, Facebook, Instagram
- AFSL verifiedZero — all unlicensed
- Loan delivered0 / 7 accounts
- MethodSherwin applied as victim to document pattern
- StatusActive — running right now
- Identity dataHarvested for resale / identity fraud
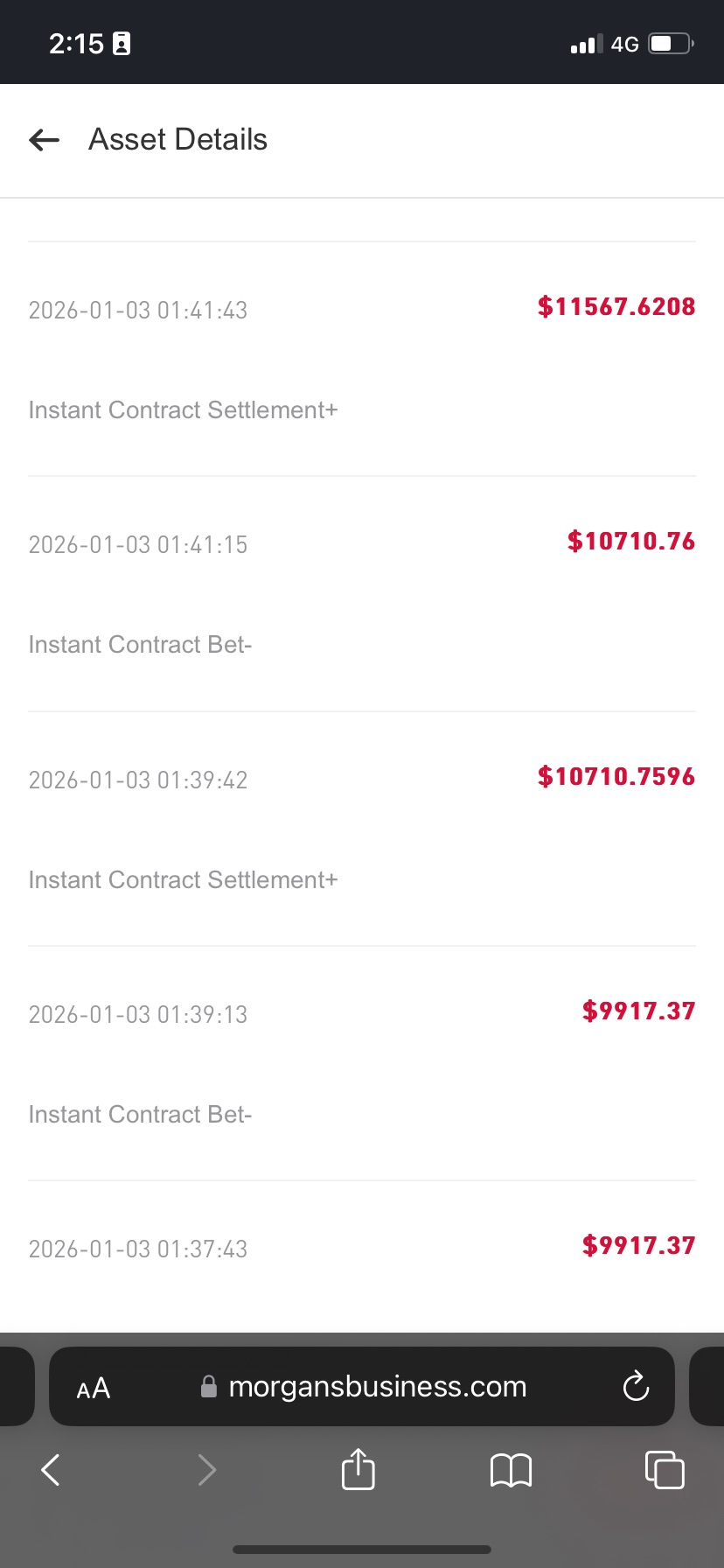
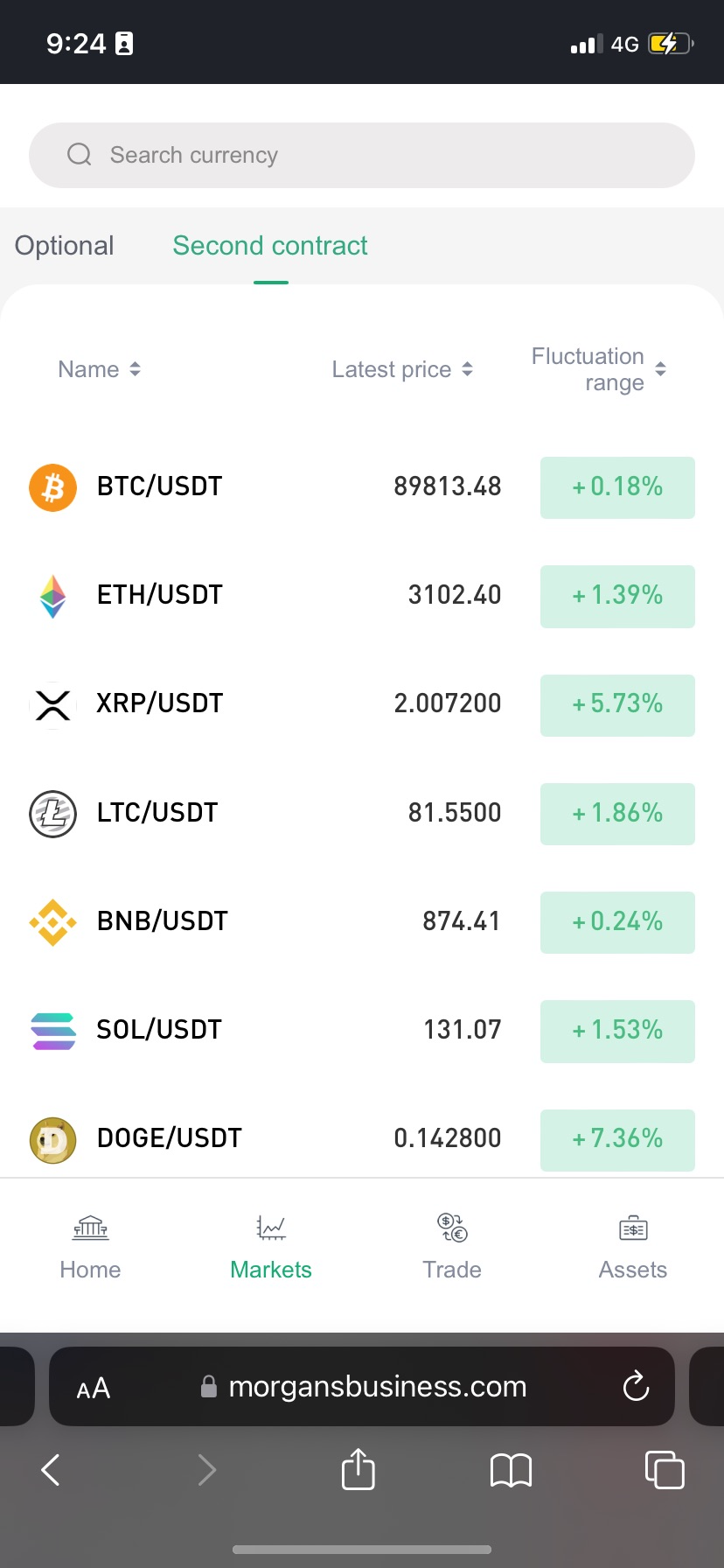
Fake Morgan Lawyers
The Second Harvest.
Fake "lawyers" impersonating the Morgan financial platform on Facebook. They target people who already lost crypto — then promise to recover $650K+ in 15 weeks for $6,500 USDT upfront. Re-victimising people who were already scammed.
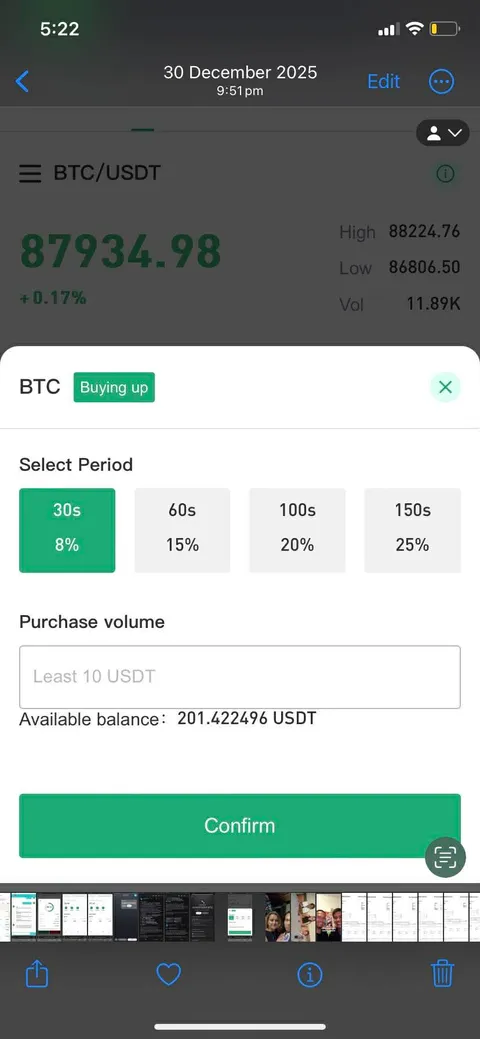

- Secondary victimization: Deliberately targets people who already lost crypto — the most vulnerable subset of scam victims
- Fake legal authority: Claims to be a law firm or attorney without any bar association registration, law licence, or court standing
- Impersonated institution: "Morgan" brand used without authorisation — ASIC register: zero match
- Advance fee demand: $6,500 USDT required before any action is taken — classic advance fee architecture
- 10,000% ROI promise: $650K+ returned from a $6.5K fee in 15 weeks — beyond any legal or financial framework
- Time pressure close: "Recovery window closes in 48 hours" — prevents victim from researching or asking anyone
- One-way valve payment: USDT only — untraceable, no chargebacks, no escrow, no legal recourse
- Zero provenance: No documented recoveries, no court cases, no clients — because no recovery ever happened
- Target profilePrior scam victims — already emotionally primed
- PlatformFacebook (targeted ads + groups)
- Entry price$6,500 USDT "recovery bond"
- Claimed recovery$650,000+ (10,000% ROI)
- Actual recovery$0 — no case in history
- Legal standingZero — impersonated institution
The victim already lost money. They're desperate, embarrassed, and looking for a solution. The scammer exploits exactly that emotional state. The hope of recovery bypasses every rational filter. They pay again — and lose again.
When Meta's AI
Became Exhibit A
Sherwin reported scams on Meta's platform to Meta's own AI. Meta AI didn't know the fraud existed on its own network. Over 98 sessions it evolved from student to self-declared exhibit — then wrote the doctrine.
See FraudShield
Detect Fraud Live
Five case studies. Every scam caught in under 300ms. A recovery scam that targets prior victims. Meta's own AI calling FraudShield "the standard." Come to Stand #33 and watch it flag in real time. Then ask: how many people lost money before anyone did?